The 3 Steps to NIST 800-171 Compliance
Published:
Feb. 20th, 2017
At this point, I’ll assume you’ve heard about NIST 800-171. You’re aware that it impacts your organization, and you know you have to figure it out before December 31st.
But where should you start?
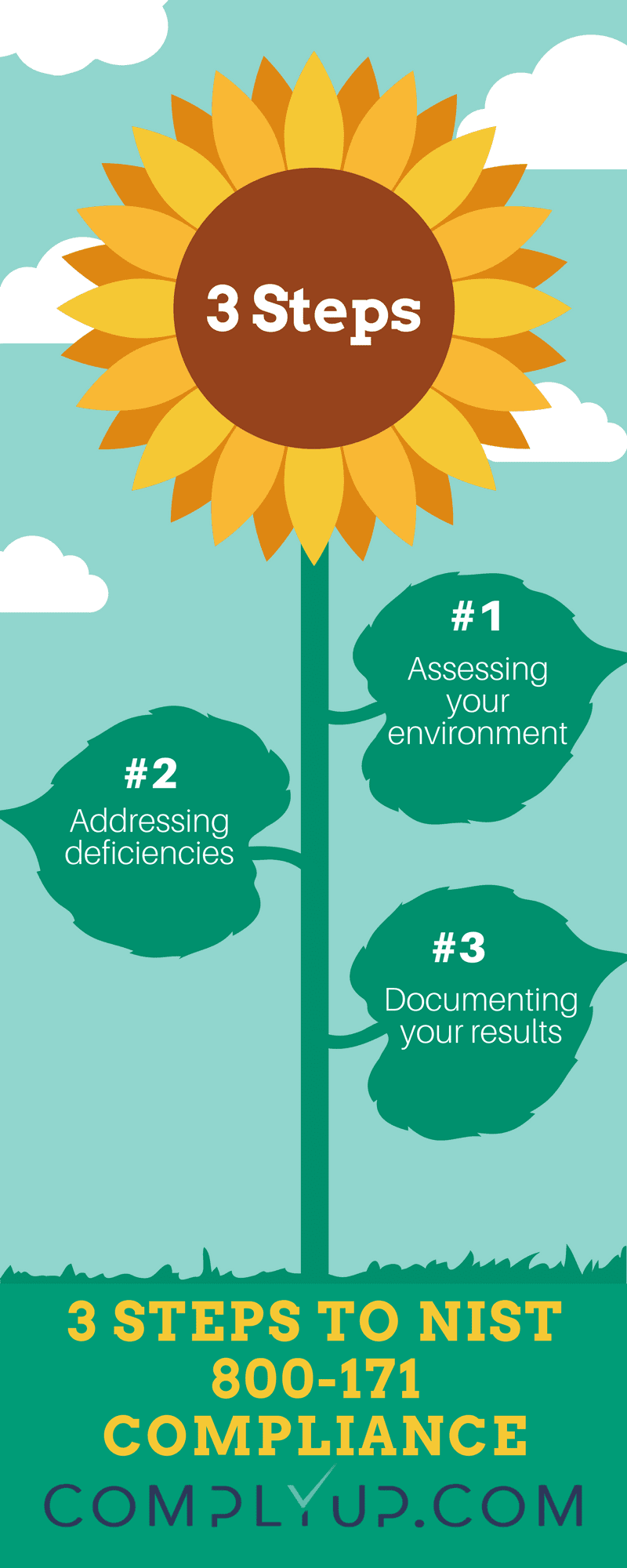
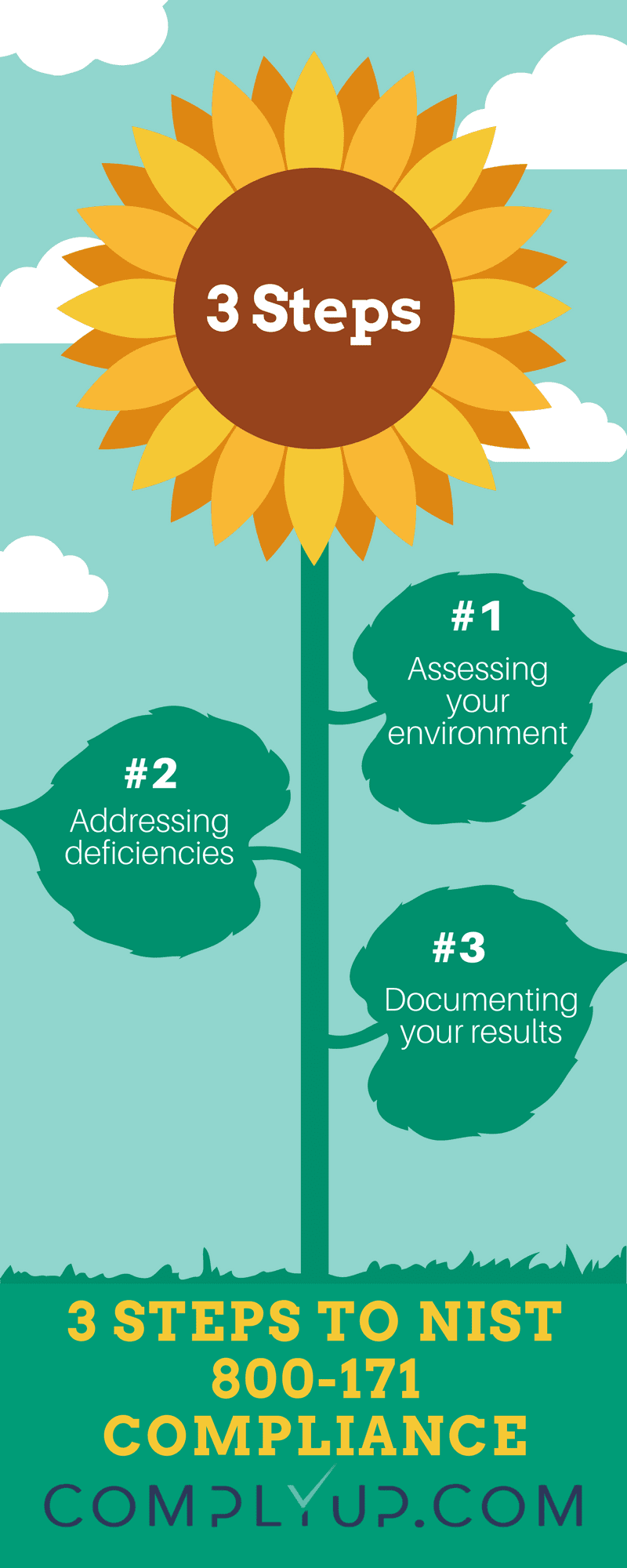
3 Steps to NIST 800-171 Compliance
It may seem daunting, but NIST 800-171 compliance can be broken down into three primary activities:
- Assessing your environment
- Addressing deficiencies
- Documenting your results
That’s basically it.
Step 1: Assessing Your Environment
First off, you need to determine which environment (or environments) are subject to NIST 800-171 compliance. Ask this question:
Does this environment process, store or transmit any Controlled Unclassified Information?
If the answer is yes, it needs to be assessed.
What exactly should you assess?
Go through the Controls (Section 3) of NIST 800-171. For each control, determine if this environment contains safeguards that satisfy the requirements.
Step 2: Addressing Deficiencies
Following your assessment, you should have a solid understanding of which controls are satisfied and which are not.
It’s time to figure out how to address the issues for each control that is not satisfied. It may be as simple as creating a policy or as complex as redesigning your network. Either way, you need to have a plan.
Step 3: Documenting Your Results
You’ve probably been documenting your activity throughout the assessment and remediation steps. At this point, it’s time to put it all together in a format that is acceptable to the Government. They’re quite particular about the way things need to be presented.
The 2 documents you need to produce
Your results should be cataloged in two specific documents:
- System Security Plan
- Plans of Action
These documents correspond to the first two steps discussed previously.
System Security Plan
The best approach for creating the System Security Plan is to create sections based on the information required in NIST 800-171.
System Security Plan Outline:
- Executive Summary
- System Boundary
- Operational Environment
- Security Requirements Implementation
- Controls 1 – 110
- Implementation Description
- Evidence Description (evidence, e.g. screenshots/documents, should be collected and saved but not necessarily included in the SSP)
- Controls 1 – 110
- Environment Interconnection with Other Systems
Plans of Action
The government is expecting you to have some issues. You’re going to raise some eyebrows if you claim to be 100% compliant.
Plans of Action Outline:
- Executive Summary
- Unimplemented Security Requirements
- Specific Controls with Issues
- Non-compliance Details
- Remediation Plan
- Specific Controls with Issues
Documentation is Key
You know how the government operates… if you deviate even slightly from their requirements you’re going to end up going back to fix things. Make sure you provide solid detail for each control and capture some sort of evidence to back it up. ComplyUp offers a comprehensive NIST 800-171 Self-Assessment Platform, complete with easy to understand explanations of each control.